DeFi’s Lose-Lose Problem on Freezing Stolen Funds

Decentralized finance (DeFi) protocols are stepping in to freeze stolen funds while centralized issuers face criticism for holding back.
A recent intervention on Arbitrum saw attacker-linked assets frozen after a major exploit, while some stablecoin issuers, including Circle, have faced public backlash for slower or more limited responses in similar situations.
Connor Howe, CEO and co-founder of cross-chain infrastructure project Enso, said that crypto protocols are not that different from centralized platforms or banks if a small group of people can freeze funds.
“The differentiation from a bank compliance officer is less than DeFi idealists will ever admit,” Howe told Cointelegraph.
The debate isn’t the usual kerfuffle between decentralization and centralization, but about who gets to intervene and how quickly they can act. In practice, it can determine whether stolen funds are stopped or slip through.
Crypto community divided on Arbitrum’s decision to freeze stolen funds. Source: Joe Hall
The limits of decentralization in DeFi
To put it simply, the industry is split on whether protocols that call themselves decentralized should be able to freeze funds during exploits.
Protocols like THORChain said they cannot freeze funds by design, even during exploits. Security researchers have questioned that claim, pointing to past cases where intervention did happen.
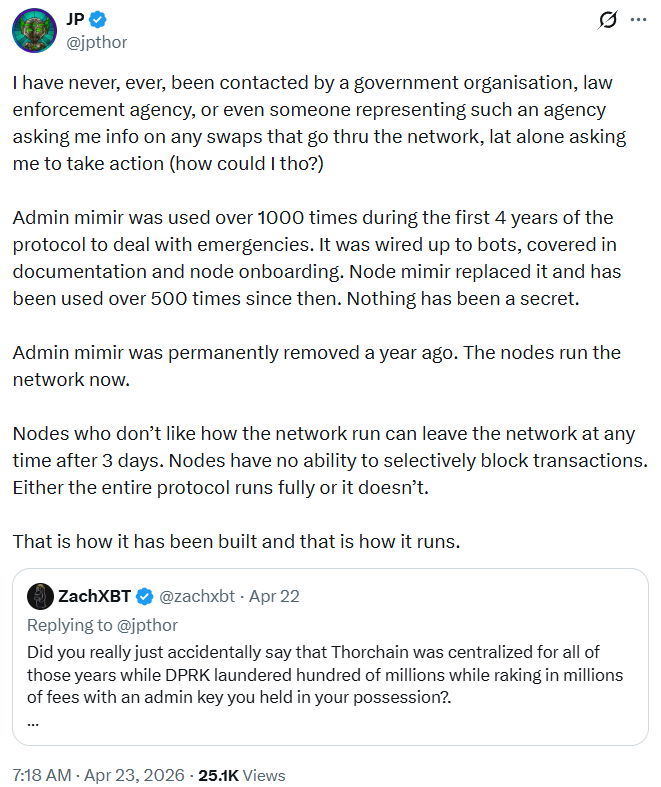
THORChain founder’s defense against the security community. Source: JP Thorbjornsen
Related: Crypto projects shut down as token models fail under pressure
Bernardo Bilotta, CEO of stablecoin infrastructure platform Stables, said the function is necessary but must operate within clear constraints.
“Freeze capabilities need to be narrowly scoped, time-limited and governed by transparent criteria that existed before the breach occurred,” Bilotta told Cointelegraph. “A protocol shouldn’t be making up the rules while the house is on fire.”
Bilotta characterized choosing “philosophical purity” over user protection as “negligence.”
The recent $293 million Kelp DAO exploit brought those discussions back into the spotlight as Arbitrum froze some of the stolen funds linked to suspected North Korean hackers. Some in the industry said the decision cut against DeFi’s grain.
The Ethereum layer-2 network has a 12-member security council with the ability to carry out certain changes to the protocol. In emergency situations, it can do so through nine of the 12 in its multisig wallet.
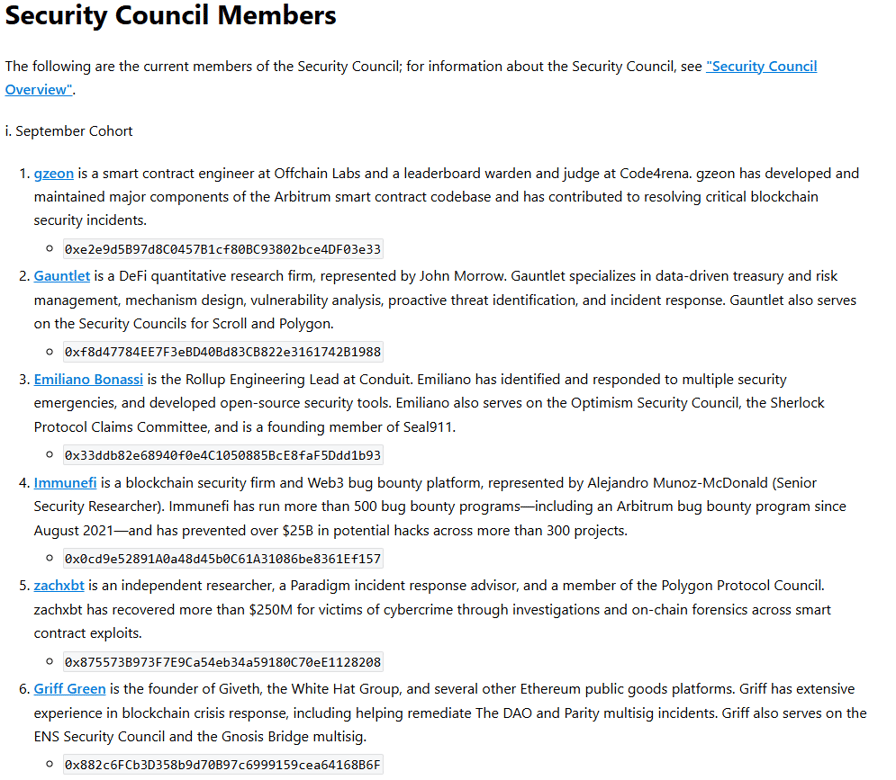
Arbitrum security council members are voted on by the network’s decentralized autonomous organization. Source: Arbitrum
Howe said that transparency in how such security councils operate can still separate DeFi platforms from traditional finance or their centralized counterparts.
“That’s notably different from a TradFi institution that invokes discretionary powers buried in their terms of service and guarded by their legal team,” Howe said.
“There should be transparency in every protocol around who holds the keys, and the safeguards in place to prevent them from going rogue. If there’s no clear distinction, then it’s a vague claim of decentralization.”
Centralized issuers face different constraints
Centralized stablecoins are among the most-traded cryptocurrencies in the world. Tether’s USDt and Circle’s USDC are the largest, accounting for more than $266 billion in combined market capitalization.
Both issuers have the ability to freeze their stablecoins, but they approach that function differently.
While Tether freezes funds more quickly in most security breaches, Circle emphasizes legal process and jurisdiction before intervening,
“Let me be clear about something that is frequently misunderstood: when Circle freezes USDC, it is not because we have decided, unilaterally or arbitrarily, that someone’s assets should be taken from them,” Dante Disparte, the company’s head of global policy, wrote in a recent blog post.
“Our ability to freeze funds is a compliance obligation — exercised only when we are legally compelled by an appropriate authority, through lawful process,” he continued.
Circle was pushed to explain its stance after the recent $280 million exploit on Solana-based Drift protocol, also attributed to North Korea.
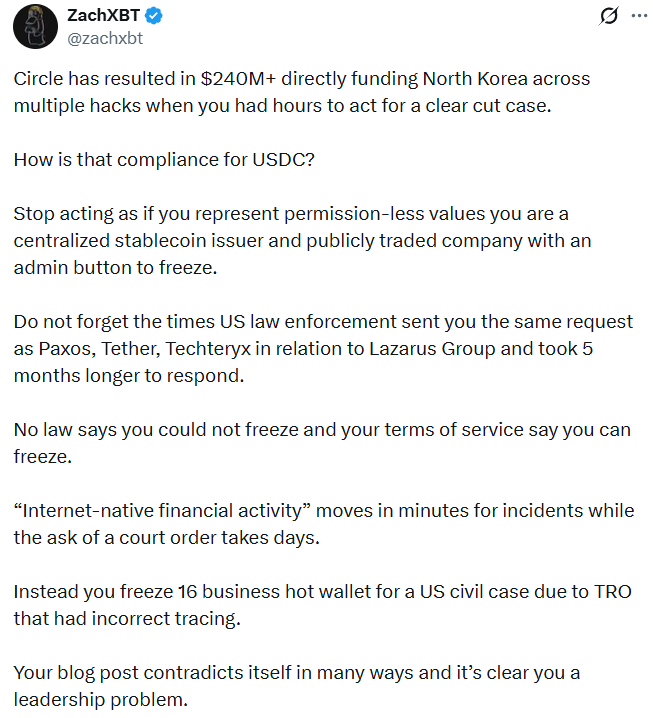
Circle’s explanation did not cut it for security experts demanding answers. Source: ZachXBT
Related: Ethereum’s EEZ could pull other blockchains into its orbit
Bilotta said waiting for formal legal orders in cases with clear, onchain evidence of an exploit is a “failure of responsibility.”
Who decides what counts as “extreme”
Large-scale exploits, including those linked to North Korean actors, have pushed the industry into situations most would consider extreme, where hundreds of millions can be drained and laundered in real time.
Such cases raise the question of who defines what qualifies as “extreme” and when intervention is justified.
“This is the question the industry has been ducking the longest,” said Wish Wu, CEO of institution-focused layer-1 Pharos.
“In practice, ‘extreme’ is too often defined after the fact by whoever holds the keys, which is exactly the failure mode decentralization was meant to avoid,” he added.
Wu said the more credible approach is to define those conditions in advance and encode them into governance, even if that means accepting that some edge cases fall outside those rules.
“Can a small, identifiable group move user funds before users have a fair chance to exit?” Wu asked.
“If the answer is yes, then whatever the marketing says, the system is custodial in substance. If the answer is no, only then are we in an honest conversation about which governance and safety tradeoffs make sense for different use cases.”
Below that line, decentralization loses its substantive meaning, he added.
Magazine: AI-driven hacks could kill DeFi — unless projects act now










